Office 2010 users, we know you're out there. As recently as 2017, according to a survey published by IT marketplace Spiceworks, Office 2010 was being used in 83 percent of the companies surveyed. But your time's up on October 13, when Microsoft officially ends support for the Office 2010 productivity suite. That means no more technical support, no more patches, and no more security updates.
As you prepare to switch, the good news is, most of the options are reasonably priced. The bad news is, each new version gets closer and closer to subscription-based products. In fact, the latest standalone version, Office 2019, exists only because enough customers complained that Microsoft relented. The writing's on the wall: Eventually, subscriptions will be the only Office option available.
 JD Sartain / IDG
JD Sartain / IDG
What happens if I stay with Office 2010?
If you are dead-set on keeping Office 2010, you can do so—as long as you’re comfortable with the risks. Because Microsoft will no longer be supporting it with bugs and patches, you will need thorough and aggressive virus protection software.
Another roadblock you may face is incompatibility with some of the newer programs and file formats. However, keep in mind that almost all Windows products can be exported regardless of one-to-one compatibility.
Should I switch to Office on the web for free?
You have one free option from Microsoft: Office on the web. All it requires is a Microsoft account. This could be a good starting point for students and new users who want to “try before they buy” and experiment with the online versions of Word, Excel, PowerPoint, and OneNote.
Keep in mind, however, that Office on the web is a limited, scaled-down version and lacks many of the full version’s features. Unless your needs are very basic you probably wouldn't want to run your business off these online applications.
Should I upgrade to Office 2019?
Office 2019 comes in three different versions and prices:
Office 2019 comes with many caveats. Unlike Office 365, which is updated regularly with new features, Office 2019 is not. You get the features that came with the original version that was released in October of 2018, and no more. Office 2019 does not include OneNote, SharePoint Designer, or InfoPath. When the next desktop version is released, you must purchase it again if you want new features.
In addition, 2019 is not supported by Windows 7 or Windows 8.1. And, for those who run networks or install software on multiple drives, Office 2019 can only be installed on the system drive—that is, the C:\ drive (usually), and that location cannot be changed.
Here's the real kicker: You must have Internet access to install and use this product, unlike 2010, which functions offline.
Should I upgrade to an Office 365 subscription?
Microsoft would love it if you upgraded to an Office 365 subscription. Obviously, instead of shelling out some money once for standalone Office, a subscription requires a monthly or yearly cash outlay.
Microsoft 365 comes in many versions, covering a wide variety of users. We'll summarize the versions below.
If you're a home or student user, you'll likely want one of these versions:
- Microsoft 365 Personal: $70 per year (or $6.99 per month)
- Microsoft 365 Family: $100 per year (or $9.99 per month)
If you need Microsoft 365 for a business, you have a longer list of packages:
- Microsoft 365 Business Basic: $5.00 per user, per month
- Microsoft 365 Apps: $8.25 per user, per month
- Microsoft 365 Business Standard: $8.25 per user, per month
- Microsoft 365 Business Premium: $12.50 per user, per month
Note: The Business Basic version provides the free Web and Mobile versions only, plus four special services: Exchange, OneDrive, SharePoint, and Teams. If you don’t need these four services, save your money and just go with the free, web-only Office 365 Online version.
In addition to the Business and Home versions, Microsoft also offers four Enterprise plans for corporations and small businesses: Microsoft 365 Apps for Enterprise, Office 365 E1, Office 365 E3, and Office 365 E5. All subscription-based, these plans provide a lot more “special services” that the other 365 plans lack.
What are my alternatives to Office?
If the whole Microsoft thing is getting too complicated or too expensive for your pocketbook, we've reviewed the major alternative programs to Office, including Google's online application, LibreOffice, FreeOffice and more. Because they're all free, there's little risk to trying them.
 Friday, February 5, 2021 at 10:42AM
Friday, February 5, 2021 at 10:42AM 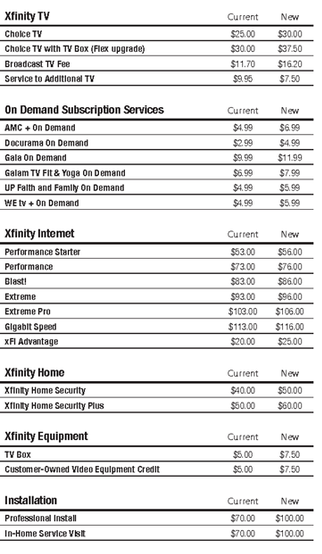
 JD Sartain / IDG
JD Sartain / IDG